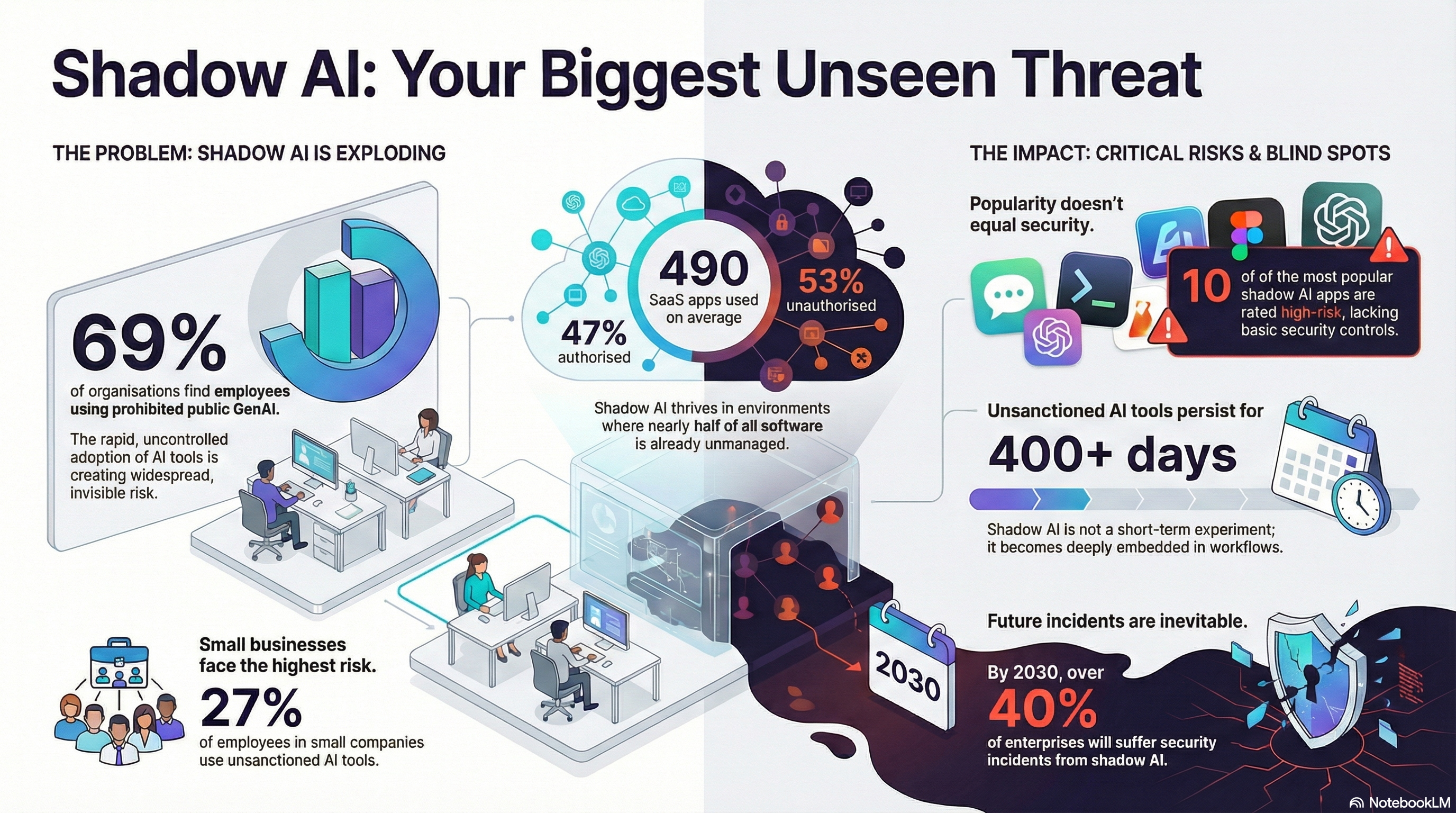
In the modern enterprise landscape, "Shadow SaaS" has transitioned from a minor IT nuisance to a dominant security challenge. Recent data reveals that organisations now manage an average of 490 SaaS applications, yet a staggering 53% of these remain unauthorised or unsanctioned by IT departments. This sprawl creates an environment where employees adopt tools for productivity—ranging from project management to generative AI—without formal security vetting, often leaving the organisation blind to massive data exposure risks. Ignoring these hidden risks is costly, as companies with high levels of shadow AI have faced data breaches costing an average of $670,000.
The Explosive Rise of Shadow AI
One of the most alarming subsets of Shadow SaaS is the rapid adoption of unsanctioned AI tools. Approximately 71% of office workers admit to using AI platforms without IT approval, often uploading sensitive company data or code into systems that may use that information to train public models. In fact, 70% of the top 10 most common AI apps have terms and conditions that allow them to utilise your organisation's data for training purposes. This "Shadow AI" creates a persistent threat; research shows that unsanctioned AI tools often remain embedded in company workflows for over 400 days before being discovered, effectively becoming a permanent part of the business infrastructure without ever passing a security audit.
Critical Security Blind Spots: Credentials and Tokens
Shadow SaaS thrives on insecure access pathways that bypass corporate Single Sign-On (SSO) and Multi-Factor Authentication (MFA). When users sign up for services using personal emails or standalone passwords, they create a massive attack surface for credential-based attacks, which account for roughly 88% of basic web application incidents. Even more dangerous is the accumulation of "offline" OAuth tokens. These persistent permissions allow third-party apps to access sensitive data long after a user has changed their password, creating a "durable token risk" that can lead to silent data exfiltration. Analysis indicates that in typical organisations, up to 52% of all tokens granted to SaaS apps are not even in active use, yet they remain high-privilege gateways into the corporate environment.
Lessons from the Field: The Cost of Misconfiguration
The risks of Shadow SaaS lead to real-world catastrophes. In 2024, the threat group ShinyHunters exploited a single misconfiguration—the lack of enforced MFA—to breach over 165 organisations through their Snowflake instances. This was not a vendor failure, but a client-side oversight where organisations failed to rotate credentials and implement strict allow-lists for their cloud environments. Furthermore, high-profile attacks like those on MGM Resorts demonstrate that even with identity providers in place, social engineering and "vishing" can be used to bypass security layers, leading to disruptions and losses exceeding $100 million.
Tutorial: How to Discover and Manage Shadow SaaS
To regain control, security teams should adopt a multi-layered discovery strategy rather than relying solely on automated scans.
Follow the Money (The Finance Audit): One of the most effective ways to find Shadow IT is through expense reports and departmental POs. If employees are paying for a subscription, they are using it. Collaborating with finance teams to flag any IT-related purchases not approved by the CISO can uncover hidden apps that network logs might miss.
Audit Your OAuth Permissions: Regularly review your identity provider (like Microsoft Entra or Google Workspace) for third-party grants. Specifically, look for apps with "offline_access" scopes combined with write permissions (e.g., mail.send or files.write). You should restrict end-user consent to verified publishers only and require admin approval for any high-privilege permissions.
Implement SaaS Security Posture Management (SSPM): Manual spreadsheets are inadequate for modern sprawl. SSPM tools provide continuous visibility into your total SaaS supply chain, which is typically 250% larger than what your direct workspace reveals. These tools can automate the remediation of misconfigurations and help ensure that departing employees are fully offboarded from all hidden accounts.
By addressing Shadow SaaS through proactive discovery and robust governance, companies can transform their cloud environments into a catalyst for secure innovation. If you are concerned about hidden risks in your stack, a professional Security Risk Assessment (SRAA) or a specialised Pentest can help illuminate these blind spots before attackers do.
Managing Shadow SaaS is like securing a large building; you might have a guard at the front door (SSO/MFA), but if employees are opening side windows (Shadow Apps) and leaving them unlocked, the front door lock becomes irrelevant.
🛡️ Ready to Strengthen Your Security?
UD is a trusted Managed Security Service Provider (MSSP)
With 20+ years of experience, delivering solutions to 50,000+ enterprises
Offering Pentest, Vulnerability Scan, SRAA, and a full suite of cybersecurity services to protect modern businesses




