Enhancing Validator Security in the Cosmos Ecosystem: The Application of Hardware Security Modules (HSMs)
In blockchain networks, validators play a crucial role. They are responsible for verifying transactions and maintaining the security and integrity of the network. The private keys of validators are used to sign blocks, making the security of these keys paramount.
Risks of Traditional Private Key Storage
In the Cosmos ecosystem, validators are tasked with validating and signing blocks to ensure the security and integrity of the blockchain. Validators typically use a password known as a private key to sign blocks. Traditionally, these private keys are stored on the local hard drive of the validator node, for example, in a file named priv_validator_key.json.
However, this storage method poses significant security risks. If the operating system is compromised by hackers, they can easily steal the private keys. Once in possession of the private keys, attackers can control the validator and potentially cause the following damages:
Double-signing attacks: Attackers can create two blocks with the same block height, thereby disrupting the consensus of the blockchain.
Slashing attacks: Attackers can take validators offline, preventing them from participating in the validation process. This could result in validators being penalized or even kicked out of the network.
To address these security issues, it is recommended that validators use Hardware Security Modules (HSMs) to store their private keys.
How HSMs Improve Security
HSMs are specialized hardware devices designed to protect sensitive data such as passwords and keys. HSMs provide multiple layers of security measures, including physical security, logical security, and cryptographic security.
In terms of physical security, HSMs typically feature tamper-resistant enclosures and anti-tampering designs to prevent unauthorized access.
In terms of logical security, HSMs use encryption algorithms and secure protocols to protect data.
In terms of cryptographic security, HSMs support various password authentication mechanisms, such as PIN codes and biometric technologies.
In the Cosmos ecosystem, HSMs can be used to store validators' private keys. HSMs store private keys in secure hardware devices rather than on computers, significantly enhancing the security of validators.
Demo Case - DecentralizedHK (DHK)
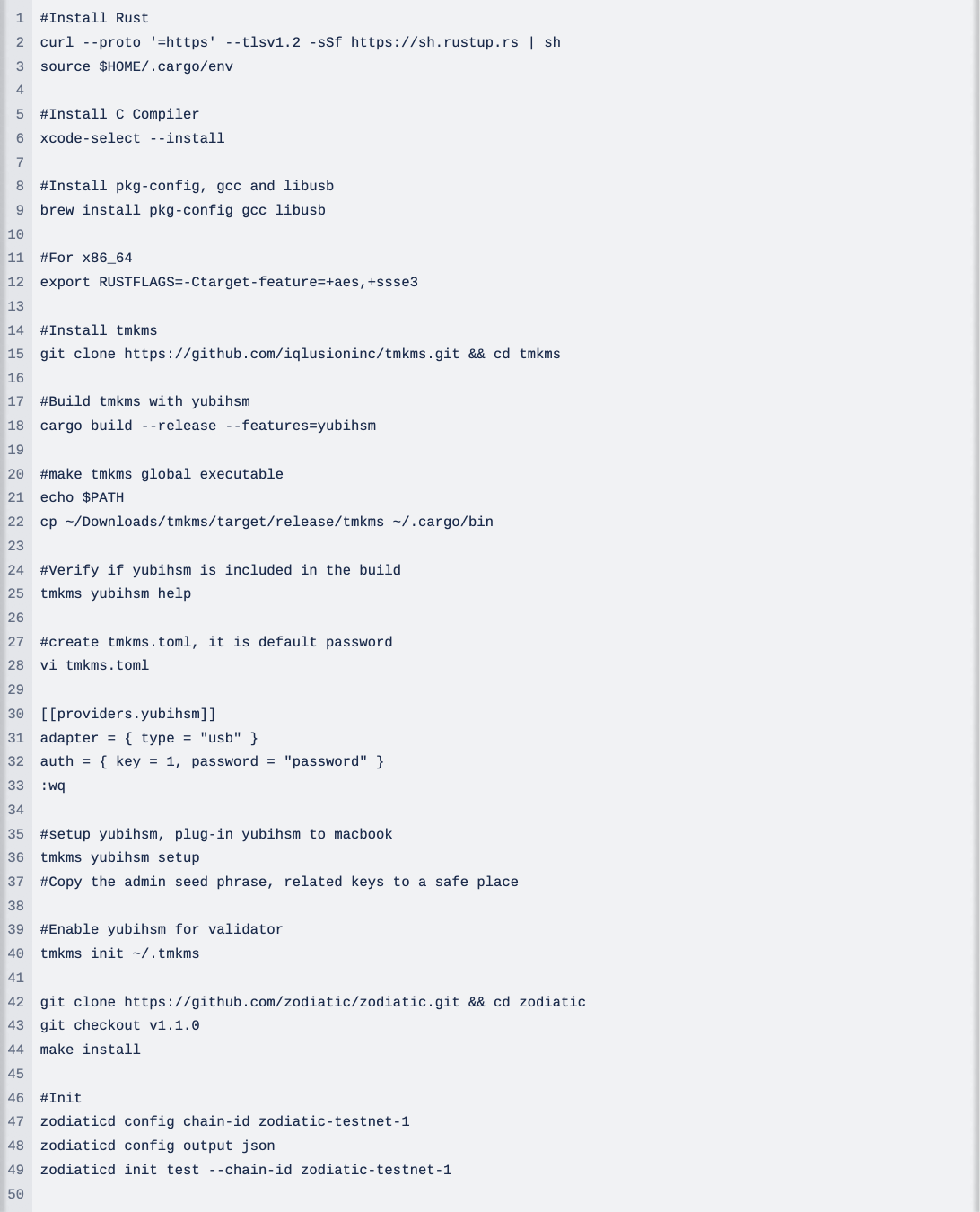
TMKMS - YubiHSM 2
Testing in Macbook(Intel i5) and using Zodiaticd v1.1.0Ref - GitHub
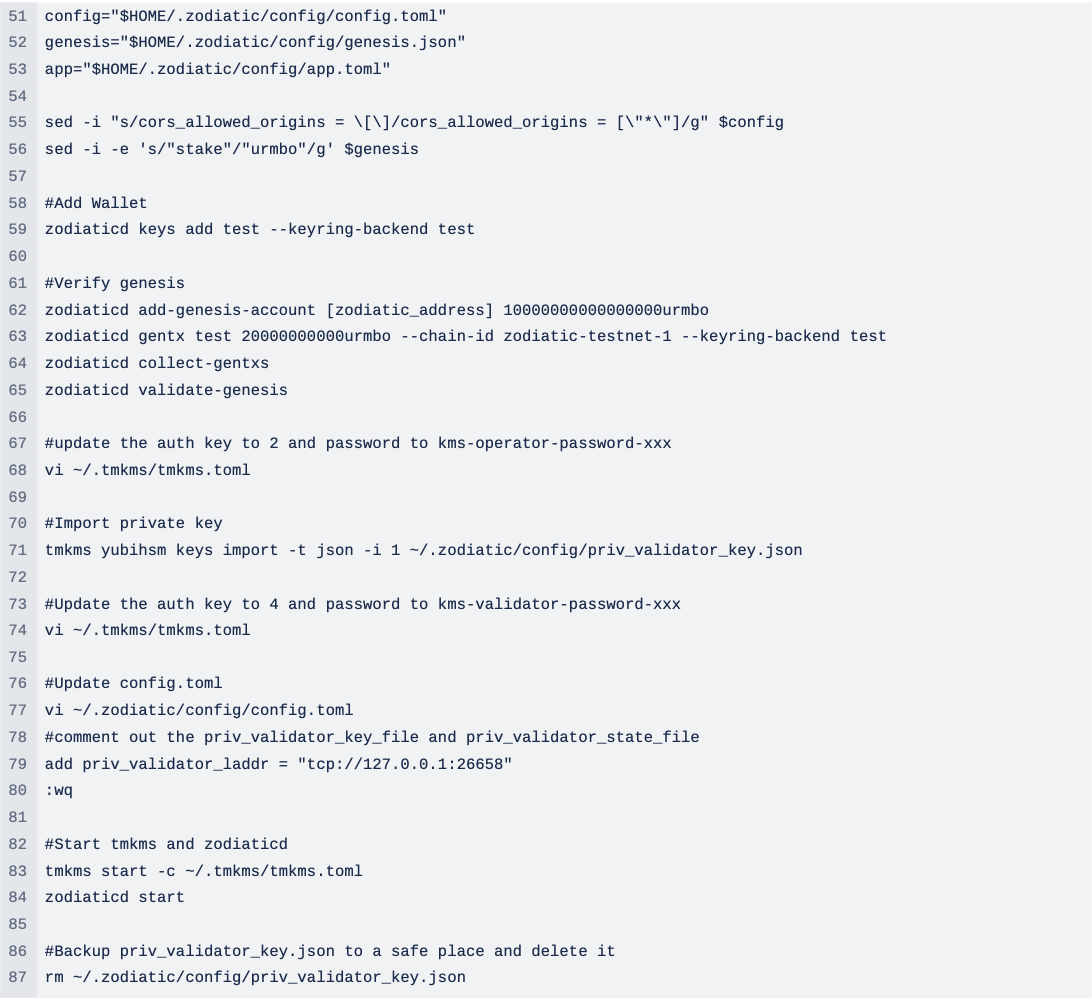
Zodiaticd successfully signing block
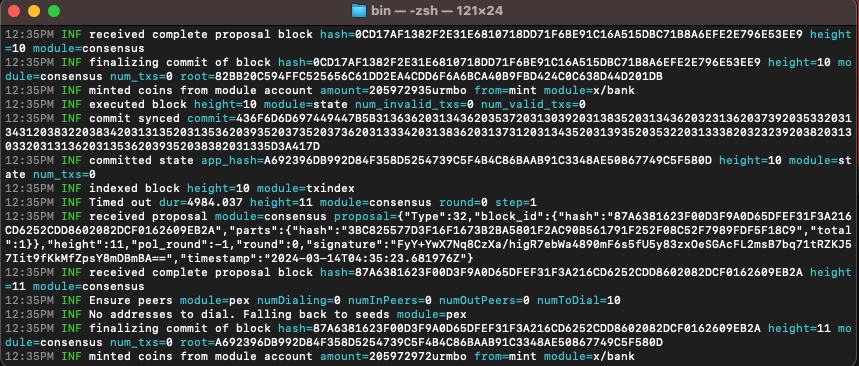
TMKMS successfully connected to Zodiaticd
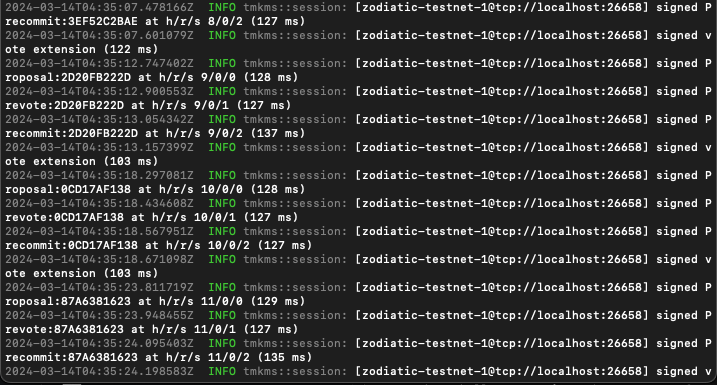
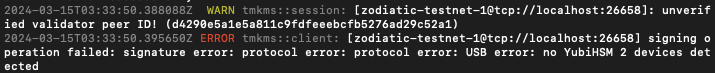
If YubiHSM accidentally unplugged
UD is a leading blockchain and security solutions provider in Hong Kong. We have over 5 years of experience in validator and node hosting, blockchain security, blockchain development, and more. Consult now and start a conversation with our blockchain team.





